The European Police Agency (Europol) formed a coalition with tech giant Intel, security expert Kaspersky Lab, and the Dutch National High Tech Crime Unit (NHTCU) to fight ransomware.
The law enforcement agencies and cyber security companies in question launched a website called No More Ransom to inform the general public about the dangers of ransomware, how to avoid it, and help victims recover their data without having to pay ransom to the cyber criminals.
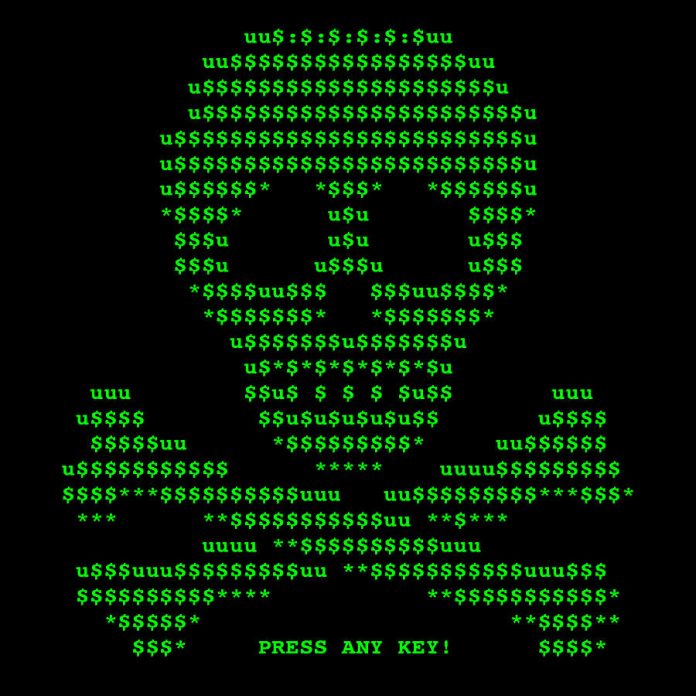
Ransomware is a version of malicious software that encrypts the victim’s data and then requests a ransom payment in return for the decryption key. In other words, it keeps the system hostage, and the only way to access is with the password the attacker provides once the victim pays, hence the name.
No More Ransom initiative
The No More Ransom website explains what ransomware is and how it works; offers advice on how to avoid or protect data from being taken hostage by ransomware. It also provides four decryption tools for different types of malware, the latest of them being specifically developed in June 2016 to combat the Shade trojan.
After Europol and the NHTCU had seized the Shade command and control server used by criminals to store keys for decryption, the keys were shared with Kaspersky Lab and Intel Security, who in turn created a unique tool. It contains more than 160,000 decryption keys and, victims can download it from No More Ransom to retrieve their data without paying.
The online initiative is set to be continually updated with more information about threats, and other security firms are being encouraged to contribute with advice or tools that can help victims of ransomware. No More Ransom currently provides decryption tools for the Shade, Coinvault, Rannoch, and Rahn families of ransomware.
A brief history of cyber kidnapping
Recent research by Kaspersky Security Network exposed the ransomware’s history and evolution, offering interesting facts and alarming figures.
In the past, the most common threat on the web was malware. Also known as malicious software, it blocked the victim’s access to an operating system or browser, until receiving a modest ransom payment.
Ransoms were mainly paid electronically, like transferring money to an e-wallet for example, and security experts, but law enforcement agencies quickly tackled the problem by changing the regulatory rules of electronic payments.
However, two years ago, cybercriminals reinvented themselves by becoming cryptors. Instead of e-wallets or such, they switched to Bitcoin, a cryptocurrency that is both a digital asset and a payment system impossible to trace or regulate and began encrypting data stored on hard drives to extort their victims.
As this files can’t be replaced by reinstalling an operating system and can’t be restored without the decryption key, the modest ransom payments transformed into huge money demands, now targeting companies and corporations as well, instead of only individuals.

Crypto-attacks are on the rise
With 120 million new ransomware samples in 2015 alone, statistics gathered by Kaspersky showed that ransomware attacks have increased like wildfires, going from 131,111 attempts to infect users in 2014–2015 to 718,536 in 2015–2016.
The ten countries with more ransomware reports are India, Russia, Kazakhstan, Italy, Germany, Vietnam, Algeria, Brazil, Ukraine, and the United States. Although the attacks in India, Algeria, Russia, Vietnam, Kazakhstan, Ukraine, and Brazil come mostly from old-school blockers, 40% of ransomware cases in the US are related to dangerous cryptors. But Italy and Germany took the worst part, with ransomware almost exclusively coming from cryptors.
The FBI has been busy too. Between April 2014 and June 2015, the agency’s Internet Crime Complaint Center (IC3) has received over 992 CryptoWall-related complaints, that have caused more than $18 million in losses.
In April 2015, the Tewksbury Police Department became the first well-known case of ransomware. Ironically, law enforcers had to pay the price to recover encrypted arrest and incident records. Earlier this year, in February, it was the turn of the Hollywood Presbyterian Medical Center. Ten days of using fax machines and paper charts drove the hospital to pay $17,000 in bitcoins, allowing employees to regain access to their computers.
https://twitter.com/brandieclaborn/status/757698629649903618
Authorities have reported new versions of ransomware
Shade and Jigsaw are two of the latest malicious software, but a new decryption key already took care of the latter. The Shade ransomware spreads via malicious websites and infected email attachments, subsequently using a sophisticated algorithm to encrypt both the data’s content and name. Kaspersky Labs and Intel Security have prevented more than 27,000 attempts since 2014.
Meanwhile, Jigsaw just debuted last April, not only encrypting files but also deleting them if the victim takes too long to decide whether to pay or not. The ransomware has gained prominence mainly due to its dark sense of humor.
Named after the main antagonist of the Saw film franchise, Jigsaw leaves a ransom note with the image of Billy the Puppet, in another reference to the movies. The message naturally delivers the iconic “I want to play a game” phrase from Billy, later explaining that the locked files are going to disappear unless the victim pays. To further pressure the target, the malware will show how much of the information it destroys every hour until there is nothing left.
The red digital clock, yet again reminiscent to Saw, marks the time left to pay before it starts deleting files. The mocking malware has also added live support to help victims obtain the bitcoins required to pay ransoms.
Although No More Ransom states that “not every type of ransomware has a solution,” it also advises victims not to give in, as they only encourage cyber criminals to continue.
Source: Kaspersky Lab