Lookout researchers recently discovered more than 1,000 spyware apps developed for Android uploaded to third-party markets and to Google Play itself. The group of apps, collectively tagged as SonicSpy, has the ability to record calls and audio, send text messages, and steal contacts and logs.
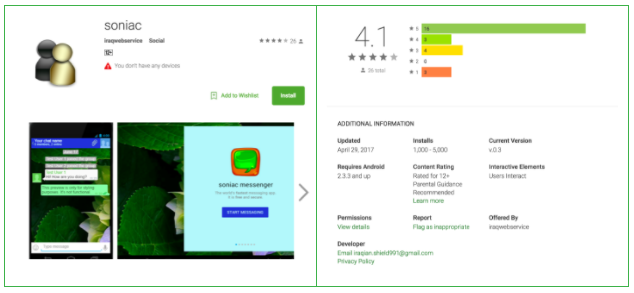
Concretely, three messaging applications have made it to the official Android store: Soniac, Hulk Messenger, and Troy Chat. Since the cyber security firm reported their discoveries to Google late last week, the apps have been removed from the platform.
SonicSpy has served as a much-needed and constant reminder of the potential dangers of mobile technology. Common sense goes a long way in protecting our devices and digital personas nowadays, so it is advised to keep out of untrusted sites to download any sort of file.
SonicSpy should be highly concerning to enterprises accessing sensitive data through mobile devices. Read more here: https://t.co/sbWG7FMijO
— Lookout (@Lookout) August 11, 2017
How do SonicSpy apps work?
According to an analysis of Soniac, the last SonicSpy app standing freely on Google Play, there are at least 73 remote functions that malicious applications of the same family can perform, all of them related to spyware tasks.
Once installed, the apps will make themselves as invisible as possible, removing their respective launcher icons from the home screen and menu while they establish an initial connection and setup with the remote server that issues their commands.
Among the most notable and dangerous functions figure the ability to record audio and calls, make calls, send text messages, snoop into logs and contact lists retrieve them, take photos with the device’s camera, and more.
Researchers have noticed that much of what is known about SonicSpy resembles another strain of malicious apps dubbed SpyNote, which first surfaced in mid-2016. Code, execution, and functionality similarities suggest that the same people are behind apps like Soniac and Troy Chat.
Iraqi hackers could be the ones responsible for this massive scheme, which mostly operates in unauthorized app markets for Android users. Soniac developers were listed as iraqwebservice and Lookout is inspecting these hints more closely.

What can users do to stay safe?
Recommendations in this scenario require a more conscious effort from users to put attention to what they are doing since it has been demonstrated once again that even Google filters can miss the occasional threat.
If you plan on installing an application make sure it is backed up by some sort of reputable statuses such as legitimate user reviews (not bots), other apps developed by them, or a distinction given by Google Play editors.
Also, it is advised to just keep it simple and download the apps you truly need and are going to use on the regular, since keeping some unused software around only to find out later that it has been compromised is a completely avoidable scenario.
Source: Lookout