
A hacker has leaked a batch of files from the security firm Cellebrite as a warning to the FBI. The data contains code from the company’s Universal Forensic Extraction Device (UFED), a tool used by governments to crack iOS, Android, and BlackBerry phones.
The leak comes after Cellebrite reported one of its servers had been breached on January 12 while undergoing maintenance.
The firm has since said the data collected by hackers contained no information that isn’t available already to their customers.
Apple has been hit with a wave of security exploits over the last few weeks, with these tools now published after taking down the iCloud Activation Lock over similar safety concerns a week ago.
What does the UFED do?
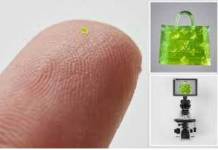
The Universal Forensic Extraction Device (UFED) is Cellebrite’s flagship product, based on a suite of desktop applications and a physical extraction device that can crack both iPhones and Android devices.
The UEFD Touch2 is one of them, which consists of a tablet-like device that connects to all kinds of phones via USB to retrieve data in them bypassing locks and security systems.
Motherboard, the outlet which first broke the story about the leaked cracking tools, reported back in December that U.S. State Police have been spending millions on these technologies through purchases of physical decoders and subscriptions to their services.
The Israeli company’s UEFD catalog is wide, and it covers products that deal with everything from extraction to analytics, passing by decoding and review of information in almost any type of smartphone.
The technology can access data from iPhones as recent as the 6 and 6S, more than 500 Android models, Windows Phone devices running Windows 8.1 or below, BlackBerry, Nokia, and GPS trackers. It can also crack tablets and Chinese chipsets like Mediatek’s.
FBI Be careful in what you wish for
Part of the data gathered and published by this or these hackers contains traces of the otherwise private UEFD software code. This has given a glimpse into the allegedly scientific Cellebrite methods to the mobile forensics community and other cyber attackers.
“IT’S IMPORTANT TO DEMONSTRATE THAT WHEN YOU CREATE THESE TOOLS, THEY WILL MAKE IT OUT. HISTORY SHOULD MAKE THAT CLEAR,” the hacker told Motherboard in an interview.
The consensus seems to be that these tools are remarkably similar to exploits and Jailbreaking systems created by hackers to bypass, for example, Apple’s rigid safety walls.
If these claims are true, they could hurt Cellebrite’s legitimacy in the industry, as it would place them at the same level as ‘common’ hackers in the eyes of notorious clients such as the governments of Russia, Turkey, and the United Arab Emirates.
Source: Motherboard










The last part of this article where you mention the effect Cellebrite’s legitimacy – I couldn’t agree more. Though I think it is goes a little further than “Cracking phones”. Even if a phone were to be jailbroken / rooted, it’s not like there’s an abundance of software out there that will just extract ALL the data from your phone. These guys are unique and one of a kind.