Police contractor and exploit development firm, Hacking Team, got hacked on Sunday July 5th. The attackers gained control of the company’s Twitter account and made 500 GB of client files, contracts, financial documents, and internal emails, some as recent as 2015, publicly available for download.
 Hacking Team, an Italian firm specialising on surveillance technology, is mainly known for its two spying software suites known as Davinci and Galileo. Hacking Team helps police spy on citizens and has clients all over the world including Ethiopia, Morocco, the United Arab Emirates, as well as the US Drug Enforcement Administration.
Hacking Team, an Italian firm specialising on surveillance technology, is mainly known for its two spying software suites known as Davinci and Galileo. Hacking Team helps police spy on citizens and has clients all over the world including Ethiopia, Morocco, the United Arab Emirates, as well as the US Drug Enforcement Administration.
The spying tools developed by the firm, have been used in many cases of privacy invasion by governments and the media.
It is not clear how much data have the hackers gained access to, but taking into account the large size of the published file, it must be a great collection of internal files.
A few hours after the firm got hacked, a list of the company’s victims was posted on Pastebin.
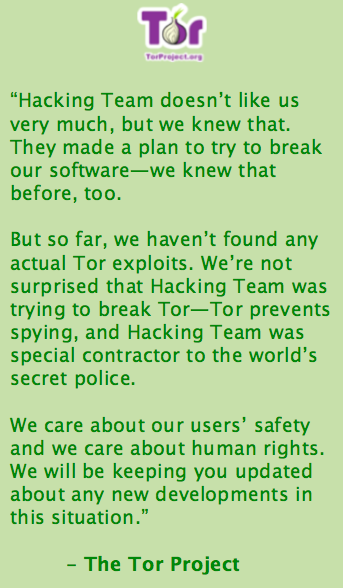
Hacking Team is infamous between security researchers because they are known to have injected malware into YouTube and Microsoft’s (NASDAQ: MSFT) Windows Live services. To do that they fraudulently obtained passport photos from the internet to get malware signing certs Hacking team also claimed that the Darknet (mainly referring to Tor) could be neutralised and decrypted, something that Tor immediately refused in a tweet.
 In one of the documents leaked, hacking team’s CEO seems to be encouraging war activities against Iran.
In one of the documents leaked, hacking team’s CEO seems to be encouraging war activities against Iran.
#HackingTeam's CEO seems to spend hours each week writing emails to their customer list encouraging bombing of Iran. pic.twitter.com/XF5FrF54jr
— Collin Anderson (@CDA) July 7, 2015
In another source code file leaked, Hacking Team seemed to be planting evidence on innocent victims. (Editor’s Notice: The Github repository was taken down while the article was being written, thus the hyperlink has been replaced with a computing.co.uk article about the evidence planting incident.)
Later that day, Hacking Team’s engineer Christian Pozzi Twitter account also got hacked revealing that the attackers will continue with attacking Hacking Team’s staff personal accounts.

Hacking Team took action asking its clients to immediately stop using its spying software. They are in “full on emergency mode“. They also noted that everyone who take place in the attack will face legal action.
Late Sunday night, security researcher known as “Phineas Fisher“, the man who last year hacked Finfisher, a German-British spyware firm took responsibility for hacking the Hacking Team’s corporate network and social accounts.
gamma and HT down, a few more to go 🙂
— Phineas Fisher (@GammaGroupPR) July 6, 2015
One of the strangest parts of the situation is that while the Hacking Team was in earlier years reffered to as the “enemy of the internet“, US media has poorly covered the recent revelations, something that could imply the liking of Hacking Team by the US government.